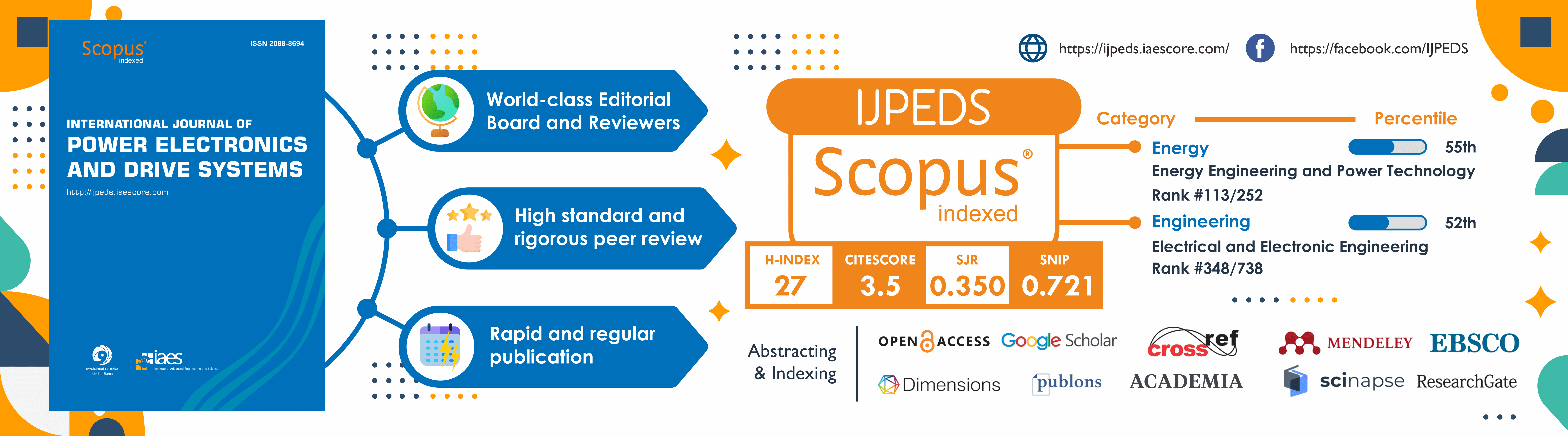
The International Journal of Power Electronics and Drive Systems (IJPEDS), p-ISSN: 2088-8694, e-ISSN 2722-256X, is the official publication of the Institute of Advanced Engineering and Science (IAES). This is a SCOPUS and ScimagoJR indexed journal, CiteScore: 3.5, SJR: 0.350, and SNIP: 0.721. The scope of the journal includes all issues in the field of power electronics, electric drives, and energy systems. Included are techniques for advanced power semiconductor devices; control in power electronics; low and high power converters (inverters, converters, controlled and uncontrolled rectifiers); control algorithms and techniques applied to power electronics; electromagnetic and thermal performance of electronic power converters and inverters; power quality and utility applications; renewable energy; electric machines; modelling, simulation, analysis, design and implementations of the application of power circuit components (power semiconductors, inductors, high frequency transformers, capacitors), EMI/EMC considerations; power devices and components; integrated and packaged; induction motor drives; synchronous motor drives; synchronous motor drives; permanent magnet motor drives; ASDs (adjustable speed drives); multi-phase machines and converters; applications in motor drives; electric vehicles; wind energy systems; solar; battery chargers; UPS; and other applications.
This journal uses a rolling submission process, allowing authors to submit at any time during the year without time restraints.
POWER UP YOUR RESEARCH: Amplify Your Impact in Power Electronics and Drive Systems
It conveys the journal's dedication to empowering researchers to enhance their research, increase their influence, and contribute to the advancement of power electronics and drive systems. IJPEDS Journal positions as a platform that supports and amplifies the impact of research in this field.
Get to Know Us Better
 |  |  |  |  |  |
| BECOMING AN AUTHOR | SUBMISSION TEMPLATE | SUBMISSION GUIDELINES | IJPEDS POLICIES | MEET OUR EDITOR | CONTACT US |
IJPEDS Guide for Authors and Template
Authors should submit only papers that have been carefully proofread and polished. Before submission, please make sure that your paper is prepared using the journal paper template <<MS Word or LaTex>>. This will ensure fast processing and publication. Any papers not fulfilling the requirements based on the guidelines to authors will not be processed.
Before proceeding with the submission, please ensure you're logged in. New users are requested to register in advance. If you'd like to know how to register as an author, you can find the complete guide here.
For more information, you can contact us at ijpeds@iaesjournal.com and ijpeds.staff@gmail.com.
Submit your paper now through Online submission ONLY.
Want to know the steps to submit your paper to IJPEDS? Catch the short guideline video!
All Issues:
- 2024: Vol. 15 No. 1, Vol. 15 No. 2, Vol. 15 No. 3, Vol. 15 No. 4
- 2023: Vol. 14 No. 1, Vol. 14 No. 2, Vol. 14 No. 3, Vol. 14 No. 4
- 2022: Vol. 13 No. 1, Vol. 13 No. 2, Vol. 13 No. 3, Vol. 13 No. 4
- 2021: Vol. 12 No. 1, Vol. 12 No. 2, Vol. 12 No. 3, Vol. 12 No. 4
- 2020: Vol. 11 No. 1, Vol. 11 No. 2, Vol. 11 No. 3, Vol. 11 No. 4
- 2019: Vol. 10 No. 1, Vol. 10 No. 2, Vol. 10 No. 3, Vol. 10 No. 4
- 2018: Vol. 9 No. 1, Vol. 9 No. 2, Vol. 9 No. 3, Vol. 9 No. 4
- 2017: Vol. 8 No. 1, Vol. 8 No. 2, Vol. 8 No. 3, Vol. 8 No. 4
- 2016: Vol. 7 No. 1, Vol. 7 No. 2, Vol. 7 No. 3, Vol. 7 No. 4
- 2015: Vol. 5 No. 3, Vol. 5 No. 4, Vol. 6 No. 1, Vol. 6 No. 2, Vol. 6 No. 3, Vol. 6 No. 4
- 2014: Vol. 4 No. 1, Vol. 4 No. 2, Vol. 4 No. 3, Vol. 4 No. 4, Vol. 5 No. 1, Vol. 5 No. 2
- 2013: Vol. 3 No. 1, Vol. 3 No. 2, Vol. 3 No. 3, Vol. 3 No. 4
- 2012: Vol. 2 No. 1, Vol. 2 No. 2, Vol. 2 No. 3, Vol. 2 No. 4
- 2011: Vol. 1 No. 1, Vol. 1 No. 2
Vol 15, No 2: June 2024
Table of Contents
|
Dalila Hadjem, Zakarya Kourdi, Salim Kerai
|
651-658
|
|
Mounir Ouremchi, Karim El Khadiri, Hassan Qjidaa, Mohammed Ouazzani Jamil
|
659-669
|
|
Bhukya Bhavsingh, Suresh Babu Gotluru, Mangu Bhukya, Ravikumar Bhukya
|
670-684
|
|
Yang Chaojun, Amberbir Wondimu, Ayodeji Olalekan Salau
|
685-695
|
|
Controlling parameters proportional integral derivative of DC motor using a gradient-based optimizer
Widi Aribowo, Reza Rahmadian, Mahendra Widyartono, Ayusta Lukita Wardani, Aditya Prapanca, Laith Abualigah
|
696-703
|
|
Usmonov Shukurillo Yulbarsovich, Sultonov Ruzimatjon Anvarjon Ugli, Mamadaliev Musulmonkul Imomali Ugli, Adeel Saleem, Kuchkarova Dilnoza Toptiyevna
|
704-714
|
|
Mohd Afifi Jusoh, Zulkifli Mohd Yusop, Aliashim Albani, Muhamad Zalani Daud, Mohd Zamri Ibrahim
|
715-724
|
|
Basima Taresh Dawood, Yasser Ahmad, Amjed Alwan Kadhim
|
725-732
|
|
Gurrala Madhusudhana Rao, B. Lakshmi Prasanna, Katuri Rayudu, Vempalle Yeddula Kondaiah, Boyanasetti Venkata Sai Thrinath, Talla Venu Gopal
|
733-743
|
|
Redouane Hachelaf, Djilali Kouchih, Mohamed Tadjine, Mohamed Seghir Boucherit
|
744-752
|
|
Gadwala Durgasukumar, Repana Ramanjan Prasad, Srinivasa Rao Gorantla
|
753-768
|
|
Rachid Boukenoui, Rafik Bradai, Aissa Kheldoun
|
769-783
|
|
Eder Alexander Molina Viloria, John E. Candelo Becerra, Dario Enrique Soto Durán
|
784-792
|
|
Eswaraiah Giddalur, Askani Jaya Laxmi
|
793-801
|
|
Ganeshan Viswanathan, Govindanayakanapalya Venkatagiriyappa Jayaramaiah
|
802-814
|
|
Ezzitouni Jarmouni, Ahmed Mouhsen, Mohamed Lamhamdi, Elmehdi Ennajih, Ilias Ennaoui, Ayoub Krari
|
815-823
|
|
Chakrapani Gandikoti, Shashank Kumar Jha, Bishnu Mohan Jha, Pankaj Mishra
|
824-834
|
|
Muhanad N. Ali, Othman M. K. Alsmadi, Ali M. Baniyounes
|
835-844
|
|
Abdessamad Benlafkih, Yassine El Moujahid, Abdelkader Hadjoudja, Nadia El Harfaoui, El-Bot Said, Mohamed Chafik El Idrissi
|
845-857
|
|
Yang Ilya Akila Abdul Rahim, Hedzlin Zainuddin, Eko Adhi Setiawan, Alfian Ferdiansyah Madsuha, Mohamad Zhafran Hussin, Shahril Irwan Sulaiman, Siti Nor Nadhirah Ibrahim
|
858-873
|
|
Neelagandan Virchuly Jyothiraman, Viraduchalam Sivachidambaranathan
|
874-882
|
|
Elmehdi Ennajih, Hakim Allali, Ezzitouni Jarmouni, Ilias Ennaoui
|
883-891
|
|
Matthew Chinedu Odo, Emenike Chinedozi Ejiogu
|
892-901
|
|
Abdelaali Ouhammam, Hassane Mahmoudi, Youssef El Hachimi, Amina Daghouri
|
902-912
|
|
Md Jahidur Rahman, Tahar Tafticht, Mamadou Lamine Doumbia
|
913-924
|
|
Ujwala Gajula, Kalpanadevi Manivannan, N. Malla Reddy
|
925-934
|
|
Meena Dhandapani, Padmathilagam Ravichandran, Arulvizhi Shanmugam, Nammalvar Pachaivanan
|
935-946
|
|
Nivethaa Thulasiraman, Lavanya Viswanathan, Palanidoss Sriramalakshmi
|
947-957
|
|
Shobana Devendiren, Samuel Rajesh Babu
|
958-967
|
|
Suroso Suroso, Hari Prasetijo, Winasis Winasis, Hari Siswantoro, Daru Tri Nugroho, Wahyu Mulyo Utomo, Afarulrazi Abu Bakar
|
968-977
|
|
Sulistyo Wijanarko, Gifari Iswandi Hasyim, Jihad Furqani, Arwindra Rizqiawan, Pekik Argo Dahono, Anwar Muqorobin
|
978-992
|
|
Annai Theresa Alphonse Arulappan, Malathi Selvaraj, Ambikapathy Aladian
|
993-1000
|
|
Elluru Ramakrishna, Gadhamappagari Jayakrishna, Sujatha Peddakotla
|
1001-1008
|
|
Ujwala Gajula, Kalpanadevi Manivannan, Nomula Malla Reddy
|
1009-1016
|
|
Nabil Driantama, Andriazis Dahono, Arwindra Rizqiawan, Jihad Furqani
|
1017-1030
|
|
Muhammad Hakiem Hayroman, Rahimi Baharom, Wan Noraishah Wan Abdul Munim, Khairul Safuan Muhammad
|
1031-1044
|
|
Angel Lichev, Yasen Madankov, Vasil Mihov
|
1045-1051
|
|
Sivasakthi Madheswaran, Radhika Panneerselvam
|
1052-1060
|
|
Ankush Babaji Aher, Sudhir Madhav Patil, Tole Sutikno
|
1061-1071
|
|
Ramavath Chander, Edara Venkata Chandra Sekhara Rao, Erukula Vidyasagar
|
1072-1080
|
|
Nishalini Delcy Arokianathan, Francis Thomas Josh, Evelyn Brindha, Jeyaraj Jency Joseph, Raman Mohan Das, Suriyan Kannadhasan
|
1081-1090
|
|
Nikita A. Dobroskok, Anastasiia D. Stotckaia, Ruslan M. Migranov, Victor S. Lavrinovskiy, Perevalov Yurii Yurievich, Artem S. Melnikov, Vyacheslav Parmenov, Nazar V. Maslennikov
|
1091-1104
|
|
Tharnisha Sithananthan, Afarulrazi Abu Bakar, Balarajan Sannasy, Wahyu Mulyo Utomo, Taufik Taufik
|
1105-1116
|
|
Davide Piumatti, Andrea Galletto, Flavio Castagno
|
1117-1127
|
|
N. Karthikeyan, S. Nanthagopal, R. Dharmaprakash, R. Ravikumar
|
1128-1136
|
|
Habib Satria, Rahmad B.Y Syah, Nukhe Andri Silviana, Syafii Syafii
|
1137-1146
|
|
Isaiah Adebayo, Yanxia Sun, Umar Awal
|
1147-1157
|
|
Siddhartha Behera, Manoj Kumar Sahu, Saroja Kumar Dash, Sarat Kumar Swain
|
1158-1166
|
|
Tahar Touahri, Brahim Berbaoui, Nouar Aoun, Slimane Laribi, Rachid Maouedj, Miloud Benmedjahed
|
1167-1177
|
|
Godslove I. Ebiega, Terdoo M. Dugeri, Ovis D. Irefu
|
1178-1189
|
|
Praveen Raj Rajaswamy Sarojam, Joseph Sarojini Savier
|
1190-1200
|
|
Ben Ali Hammoudi, Hicham Serhoud
|
1201-1210
|
|
Ganesapandiyan Ponkumar, Subramanian Jayaprakash, Dharmaprakash Ramasamy, Amudha Priyasivakumar
|
1211-1217
|
|
Nur Afiqah Hani Senin, Iskandar Dzukarnain Rummaja, Muhammad Idzdihar Idris, Zul Atfyi Fauzan Mohammed Napiah, Radi Husin Ramlee, Marzaini Rashid, Luke Bradley
|
1218-1226
|
|
Yerragolla Hazarathaiah, B. Venkata Rami Reddy
|
1227-1234
|
|
Ilham Tyass, Abdelouahed Bellat, Abdelhadi Raihani, Khalifa Mansouri
|
1235-1246
|
|
Supriya Jayaprakash, Rajashekar Jangam Siddamallaiah
|
1247-1253
|
|
Tonmoy Hassan, Debraj Das, Shahir Islam Rhyme, Supratik Bal, Md. Rifat Hazari, Effat Jahan, Chowdhury Akram Hossain, Mohammad Abdul Mannan
|
1254-1265
|
|
Mothala Chandrashekhar, Pradyumna Kumar Dhal
|
1266-1275
|
|
Arathi Pothakanahalli Bhemasenarao, Shankaralingappa Channappa Byalihal
|
1276-1289
|
|
El-Zahraa M. Mattar, Ekramy S. Mahmoud, Mohammed Ibrahim El-Sayed
|
1290-1299
|
|
Mazyed A. Al-Tak, Mohd Fadzil Ain, Omar Sh. Al-Yozbaky, Mohamad Kamarol Mohd Jamil
|
1300-1307
|
|
Supapong Nutwong, Nattapong Hatchavanich, Anawach Sangswang, Ekkachai Mujjalinvimut, Mongkol Konghirun
|
1308-1318
|

